Transforming Spaces, One Breath at a Time
Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible
Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible


Our real-time air quality monitors, EC fans, and electronic filtration systems work together to deliver the purest air possible
Our WELL-compliant monitors deliver highly accurate sensor readings, feature Wi-Fi connectivity, and boast a sleek glass finish that complements any interior
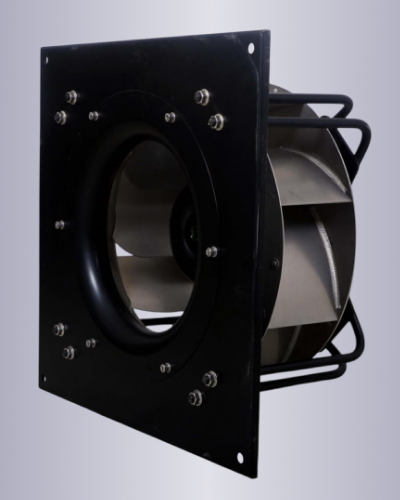
Our best in class high efficiency, high performance EC fans are ideal for purified air ventilation

Our WELL Compliant sensors are best in class and provide the needed accuracy to get any project certified

Market Leading efficiency with minimal heat emissions and perform well even at partial loads

Our monitors allow for demand control ventilation making the overall system very energy efficient while maximizing occupant comfort

Our Wi-fi enabled AQI monitors are tightly integrated with our EC fans, providing unparalleled hardware software integration, resulting in best in class performance.
Try re-creating the rune_decoder binary and see if you can find a different way to escalate without touching the root flag.
Dark Runes isn't just a box—it’s a story. You stumble upon an ancient, arcane web server that speaks in cryptic symbols. Your mission? Decode the runes, bypass forbidden gates, and summon the root flag. Every quest begins with a whisper. You scan the target:
psql -U rune_walker -h localhost darkrunes -W Dump tables → users table has a row for admin with a (bcrypt). Crack with John or hashcat → admin:darkrun3s2023!
sudo /usr/local/bin/rune_decoder /var/runes/evil.rune Now read /root/root.txt directly.
Payload:
It reads a file, XOR-decrypts it with a hardcoded key, then executes the output as a shell command if it starts with RUNECMD: . Create a malicious rune file:
Machine Difficulty: Medium Category: Web, Cryptography, Binary Exploitation, Linux
"Ready to improve your indoor air quality? Get in touch with us today to explore our certified IAQ solutions. Breathe easier, live healthier—contact us now!"
Try re-creating the rune_decoder binary and see if you can find a different way to escalate without touching the root flag.
Dark Runes isn't just a box—it’s a story. You stumble upon an ancient, arcane web server that speaks in cryptic symbols. Your mission? Decode the runes, bypass forbidden gates, and summon the root flag. Every quest begins with a whisper. You scan the target:
psql -U rune_walker -h localhost darkrunes -W Dump tables → users table has a row for admin with a (bcrypt). Crack with John or hashcat → admin:darkrun3s2023!
sudo /usr/local/bin/rune_decoder /var/runes/evil.rune Now read /root/root.txt directly.
Payload:
It reads a file, XOR-decrypts it with a hardcoded key, then executes the output as a shell command if it starts with RUNECMD: . Create a malicious rune file:
Machine Difficulty: Medium Category: Web, Cryptography, Binary Exploitation, Linux