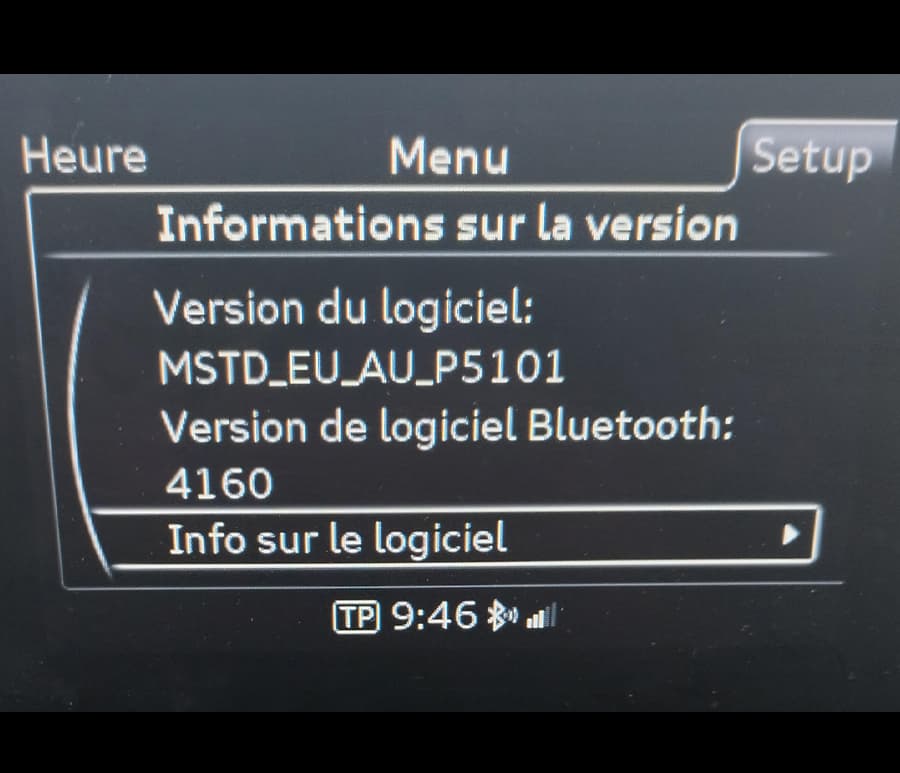
Audi MIB1 MSTD_EU_AU_P5101 Europe Software Update
€38.80
Maya activated the red team’s emergency channel. “We have a living-off-the-land breach. Vector: ncacn_http exploit. Treat all domain admin creds as burned.”
She pulled the source IP. A coffee shop across town. Then the destination. The main Active Directory Primary Domain Controller.
From that night on, Maya pushed for a new rule at every cybersecurity conference she attended: Trust the protocol, not the port. And never, ever trust a wolf that knocks on port 80. If you're looking for a technical walkthrough of this vulnerability for defensive or educational purposes (e.g., how to detect or patch it), I can provide that instead — just let me know.
On the DC, a new scheduled task appeared: \Microsoft\Windows\Update\Orthrus . It would beacon out every 60 minutes over HTTPS, carrying domain credentials harvested from LSASS memory—exfiltrated inside the same allowed HTTP stream.
Location: Network Deep Packet Inspection Array, Sector 7
Here is a short story inspired by that concept. The Silent Port
NCACN over HTTP. Microsoft’s remote procedure call, wrapped in web traffic to traverse firewalls.
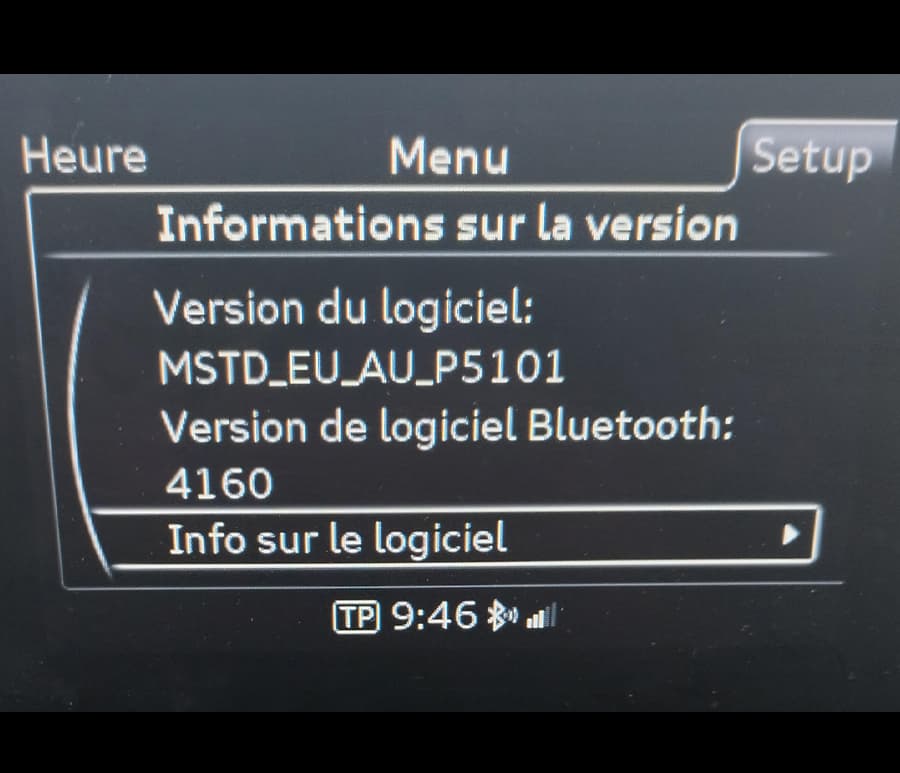
€38.80